As the popularity and development of smart phones, the requirements on wireless network coverage is becoming increasingly prominent. The network coverage of GSM/3G/4G can not meet the customer's rate requirements in many areas, and can not meet the business needs of certain specific scenarios. WiFi coverage can not only meet the user's speed requirements, but also meet the customized needs of specific areas.
Shanghai Chucheng Information Technology Co., Ltd. is committed to creating multi-scenario wireless coverage solutions to ensure wireless network access security, no blind area on coverage, and provide various of customized services.
Specialty of CCIT WLAN solution
Excellent network security of wireless
1. Elaborate access control policies multi-dimensional admission mechanisms such as terminals, identities, etc. to ensure that only legitimate terminals can access;
2. VLANs can be flexibly assigned to support network user isolation based on ports, terminals, and identities, ensuring the security of intranet information;
3. Combine the communication tunnel and transmit data encryption function to effectively prevent network data from being captured and tampered;
4. The built-in enterprise firewall, WIPS/WIDS system, effectively prevent hacking attacks, and ensure the security of enterprise data.

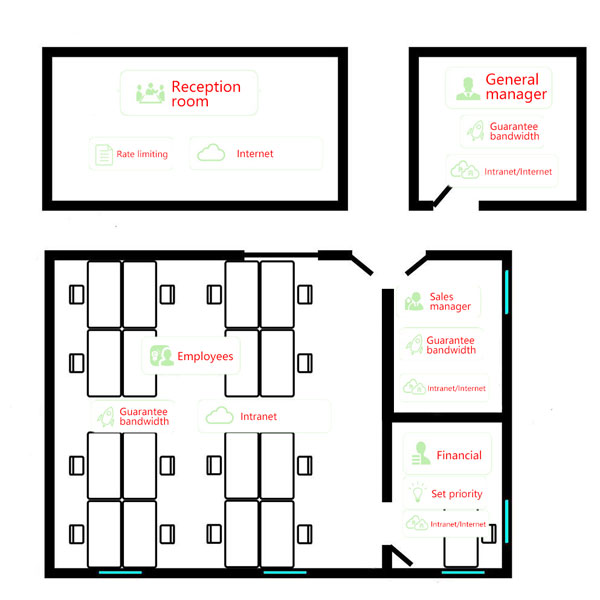
Elaborate network permission settings
Various network permissions can be defined and set different network permissions for different roles.
Customized services
Scenic spot:

Shopping mall:
1. The built-in advertising push center supports personalized marketing advertisements according to different terminals, time slots, locations, and access times.
2. The function of internet behavior analysis can understand the user's search preference according to internet behaviors, and perform accurate advertisement pushing.
3. Comprehensive analysis of passenger flow data based on a custom period, can get statistics on the flow of people in each region, the number of new users, the return rate, and the time of residence.
4. The user's portrait function automatically collects information such as visiting preferences, frequency, terminal type, visitor area, user tags, and activity trajectory, and supports single user portrait query;

Hotel:
Hotel Marketing

Enterprise:
1. The built-in flow control function can divide traffic for applications, users, and regions, ensure the bandwidth of key services, and increase the value of bandwidth utilization.
2. Air interface resource management based on application, flexible identification of online activities such as office, entertainment, video, and download, giving priority to securing office bandwidth.

Network topology of different solution
Enterprise

Hotel

Shopping mall

Education

Hospital


 CN
CN EN
EN


